This document provides a deep technical explanation of how the Duplicate Killer WordPress plugin implements cookie-based logic to assist with duplicate form submission prevention.
It is written for developers, agencies, and advanced WordPress users who want to understand exactly how the system behaves at runtime.
WordPress form plugins do not enforce uniqueness constraints. The same browser can submit identical values multiple times, intentionally or accidentally.
Duplicate Killer addresses this problem using a multi-layered strategy:
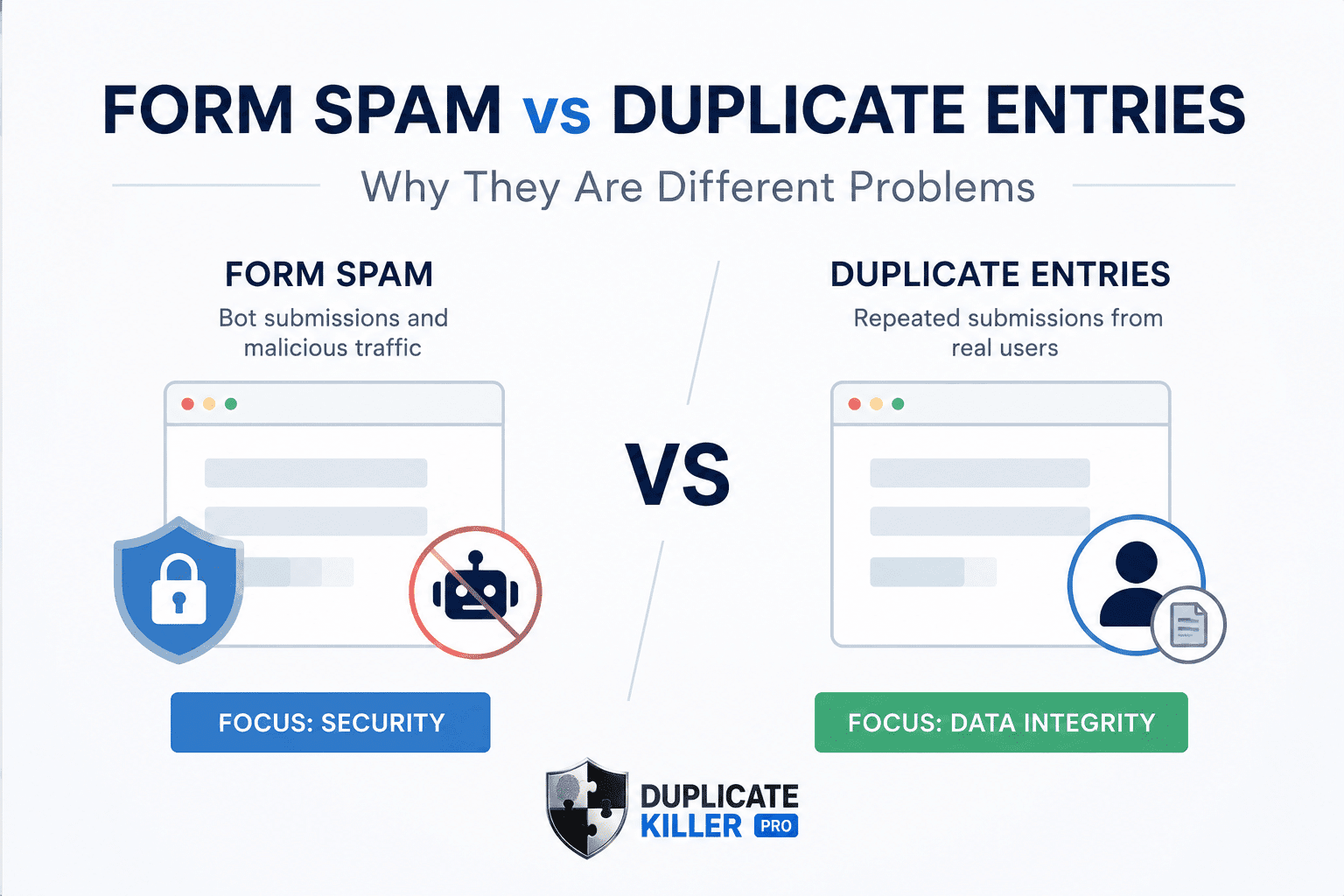
The cookie system is not a security feature. It is a context signal.
The cookie system follows these strict rules:
Each cookie answers only one question:
“Has this browser already submitted this exact form?”
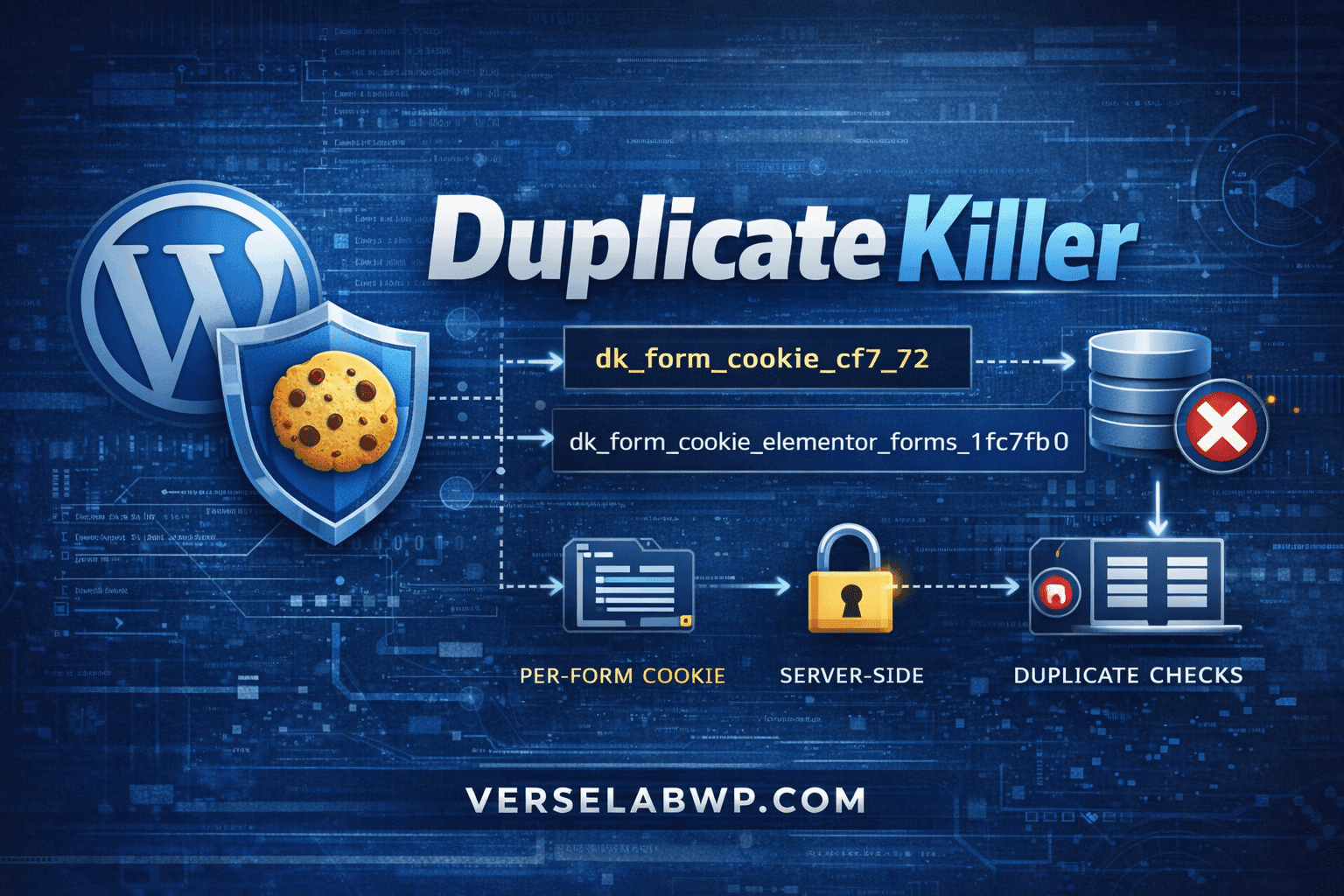
Cookies are generated using a deterministic naming scheme:
dk_form_cookie_{provider}_{form_id}Examples:
dk_form_cookie_cf7_72
dk_form_cookie_elementor_forms_1fc7fb0
dk_form_cookie_forminator_92
dk_form_cookie_wpforms_96
dk_form_cookie_formidable_contact-us_2
This guarantees:
Duplicate Killer injects a single external JavaScript file. No inline scripts are used (CSP-safe).
DOM Ready
↓
Scan for supported form selectors
↓
Extract provider-specific form identifier
↓
Check allowlist (PRO configuration)
↓
Set cookie if allowed
function setCookie(name, days) {
if (document.cookie.includes(name + '=')) return;
const token = Date.now().toString(36) + Math.random().toString(36).slice(2);
const expires = new Date(Date.now() + days * 86400000).toUTCString();
document.cookie =
name + '=' + encodeURIComponent(token) +
'; expires=' + expires +
'; path=/; SameSite=Lax';
}
Important details:
Each WordPress form plugin exposes form identifiers differently. Duplicate Killer handles this explicitly.
var cf7 = formEl.querySelector('input[name="_wpcf7"]');
return cf7 ? parseInt(cf7.value, 10) : null;
var ef = formEl.querySelector('input[name="form_id"]');
return ef ? ef.value.toLowerCase() : null;
var hidden = formEl.querySelector('input[name="form_id"]');
return hidden ? hidden.value.toLowerCase() : null;
Notice:
Cookies are created only if the form is explicitly enabled in the database.
$providers['cf7'] = [
'enabled' => true,
'cookie_prefix' => 'dk_form_cookie_cf7_',
'per_form_days' => [
72 => 7,
71 => 3,
],
];
If a form ID is missing from per_form_days, no cookie is created.
This prevents:
Cookies are read during validation and save hooks.
function dk_get_form_cookie_simple(array $options, string $form_name, string $cookie_prefix): array {
$form_cookie = 'NULL';
$checked_cookie = false;
if (!isset($options[$form_name]['cookie_option']) ||
$options[$form_name]['cookie_option'] !== '1') {
return compact('form_cookie', 'checked_cookie');
}
$form_id = (string) $options[$form_name]['form_id'];
$cookie_name = $cookie_prefix . sanitize_key($form_id);
if (!empty($_COOKIE[$cookie_name])) {
$form_cookie = sanitize_text_field(wp_unslash($_COOKIE[$cookie_name]));
$checked_cookie = true;
}
return compact('form_cookie', 'checked_cookie');
}
This ensures:
The cookie value is passed into database checks:
duplicateKiller_check_duplicate_by_key_value(
'elementor',
$form_name,
$field_key,
$submitted_value,
$form_cookie,
$checked_cookie
);
The database layer can then decide:
Deleting cookies does not disable Duplicate Killer.
Cookie creation happens once per form per browser. Runtime cost is negligible.
The Duplicate Killer cookie system is intentionally minimal, explicit, and deterministic. It exists to support duplicate submission prevention, not to replace proper backend validation.
This architecture ensures predictable behavior across WordPress form plugins while remaining privacy-conscious and performant.